Traditional Security Information and Event Management (SIEM) solutions have been the go-to approach for organizations to collect, analyze, and manage security events and logs. However, SIEM solutions often struggle to keep pace with the rapidly evolving threat landscape and the complexity of modern cyber-attacks. They lack advanced threat detection capabilities, leaving organizations vulnerable to sophisticated threats that evade traditional signature-based detection methods. The size and complexity of big data have also made most SIEMs incapable of effectively collecting, analyzing, and correlating data from multiple sources and at high scale. These limitations hinder timely incident response, increase the risk of undetected breaches, and weaken overall security effectiveness.
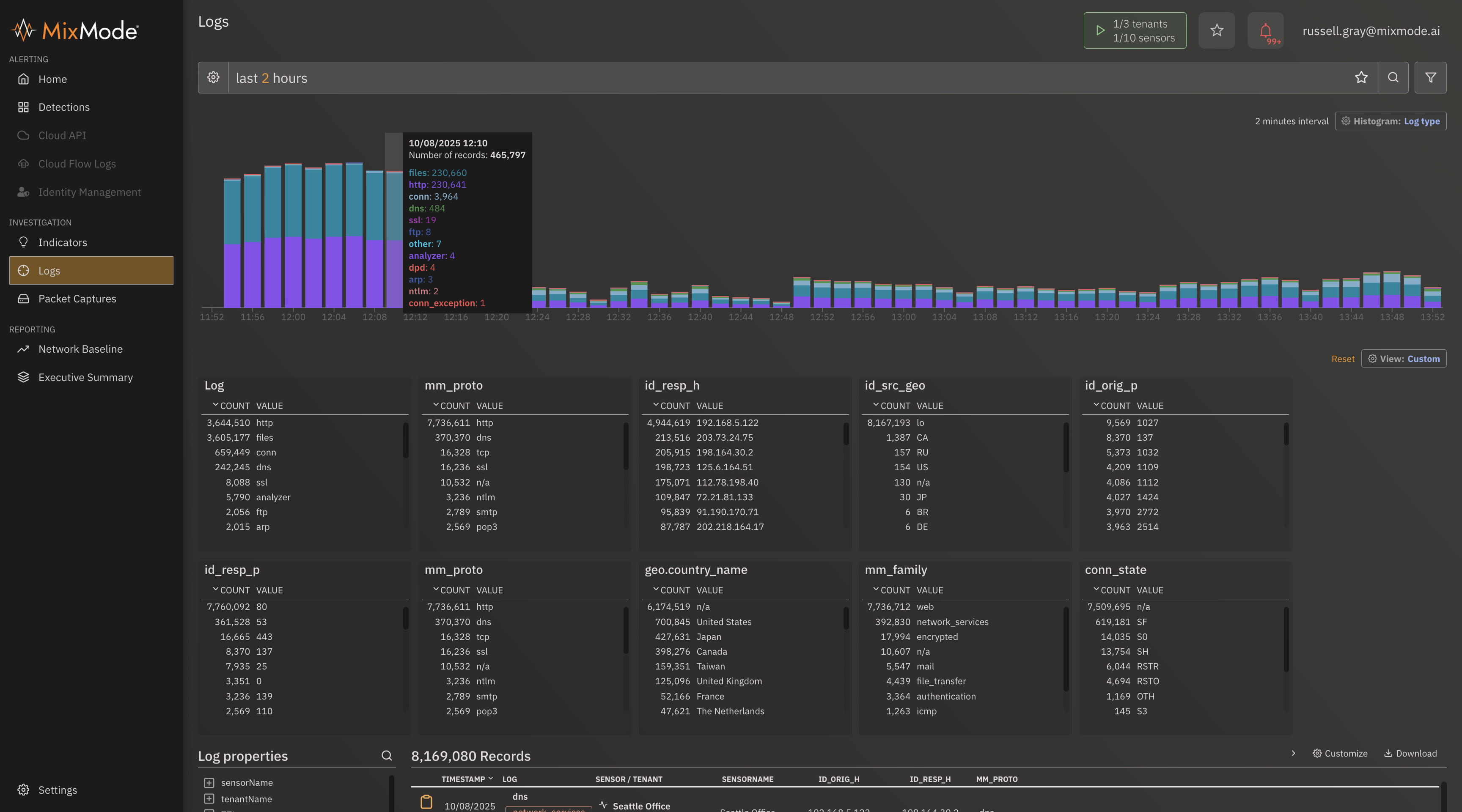
The MixMode Platform helps enhance a SIEM’s capabilities by ingesting and analyzing large volumes of data in real-time, automating the threat detection process to drastically reduce false positives and surface relevant threats. This enables analysts to do more with less and save time by focusing on the threats that matter.
The MixMode Platform helps enhance existing investments, maximizing ROI and delivering long-term value. By leveraging AI-driven detection alongside a SIEM, organizations can strengthen their cybersecurity posture, enhance threat detection and response capabilities, and stay ahead of rapidly evolving cyber threats.
Click the button below to download the Platform Data Sheet.