Misconceptions of the SOAR “Playbook”

The following is an excerpt from our recently published whitepaper, “SOAR: The Acknowledgement That All of Your Cybersecurity Platforms Have Failed,” in which we explain why the patchwork strategy of additive cybersecurity solutions and technology is failing in the modern threatscape and why we believe SOAR is just an admission that all of your other cybersecurity platforms aren’t doing their job.
Misconceptions of the SOAR “Playbook”
Most customers are surprised to learn that SOAR platforms rely on invoking 3rd party technologies, including next-generation firewalls and endpoint protection platforms via traditional API calls to isolate and quarantine malicious threats and users.
The ability to invoke those API calls is a product of months — sometimes years — of highly manual workflow definition and continuous refinement to create what SOAR vendors call “playbooks.”
During this process, SOAR vendors downplay the common customer misconception that the O (“Orchestration”) and the A (“Automation”) in SOAR are adjectives for the R (“Response”).
That assumption is categorically incorrect. SOAR technology is neither designed nor intended to independently execute, orchestrate and automate response or remediation. SOAR platforms are designed as workflow tool sets capable of automating information sharing and correlating data and events between legacy silos, applications and incomplete data sources.
However, they are reliant on third party platforms and human operators to take action.
“SOAR is designed to stitch together disparate platforms and data sources that don’t play well together, but that’s not how they are sold,” explains Geoffrey Coulehan, Head of Sales and Strategic Alliances at MixMode. “Vendors and analysts propagate the idea that somehow, theoretically, the creation of playbooks and workflow processes across disparate vendor platforms is going to deliver an improved or automated response to the most serious threats and vulnerabilities, which has not proven valid in today’s environment.”
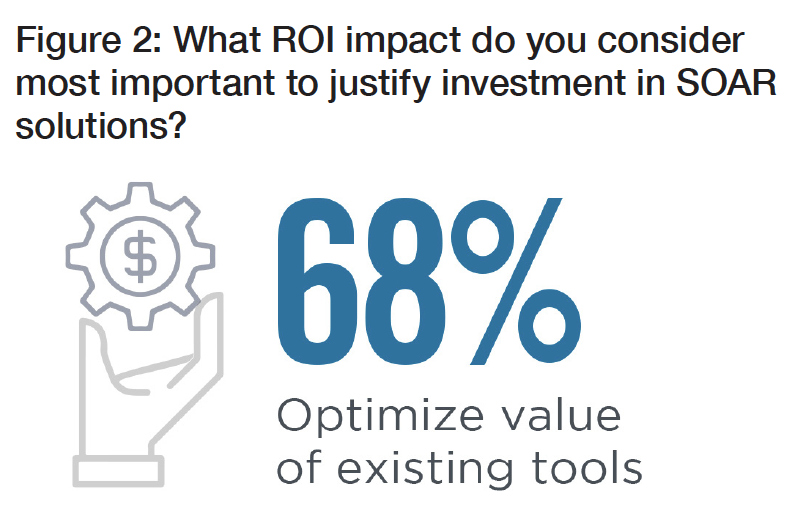
In Swimlane’s 2020 SOAR Report, 68 percent of cybersecurity professionals also stated that the most valuable functionality of their SOAR platform is its ability to optimize existing tools (i.e. SIEM, NDR, and EDR). See Figure 2. This implies that without such tools, their SOAR wouldn’t be able to perform its most important function.
Still not convinced? Consider Gartner’s own definition, which states that a SOAR platform “informs decisions by correlating the output of siloed processes and technologies.”


