MixMode Now Supports Amazon VPC Flow logs
We’re excited to announce the general availability of support for Amazon Web Services’ VPC Flow Logs, in the MixMode platform!
MixMode prides itself in offering a heterogeneous, “single pane of glass” view and analysis into multiple kinds of workloads, including both On-Premise and Cloud workloads.
As we mentioned in a previous blog post about monitoring AWS CloudTrail, the challenge with workloads in cybersecurity is twofold. First, the tools log every call into your account(s) so logging can be quite voluminous. In fact, one resource places the signal to noise ratio of CloudTrail events to be about 1:25,000. Second, the logs produced are not susceptible to traditional security detection via intelligence feeds, attack signatures or hash values. As such it can be difficult to know parse potential threats from normal behaviors.
VPC Flow Log support now allows MixMode to guard your Amazon EC2 workloads, as a complement to On-Premise workloads as well as Amazon API workloads (using CloudTrails).
AWS VPC Flow Logs are easy to set up, using the AWS control panel, as shown below:
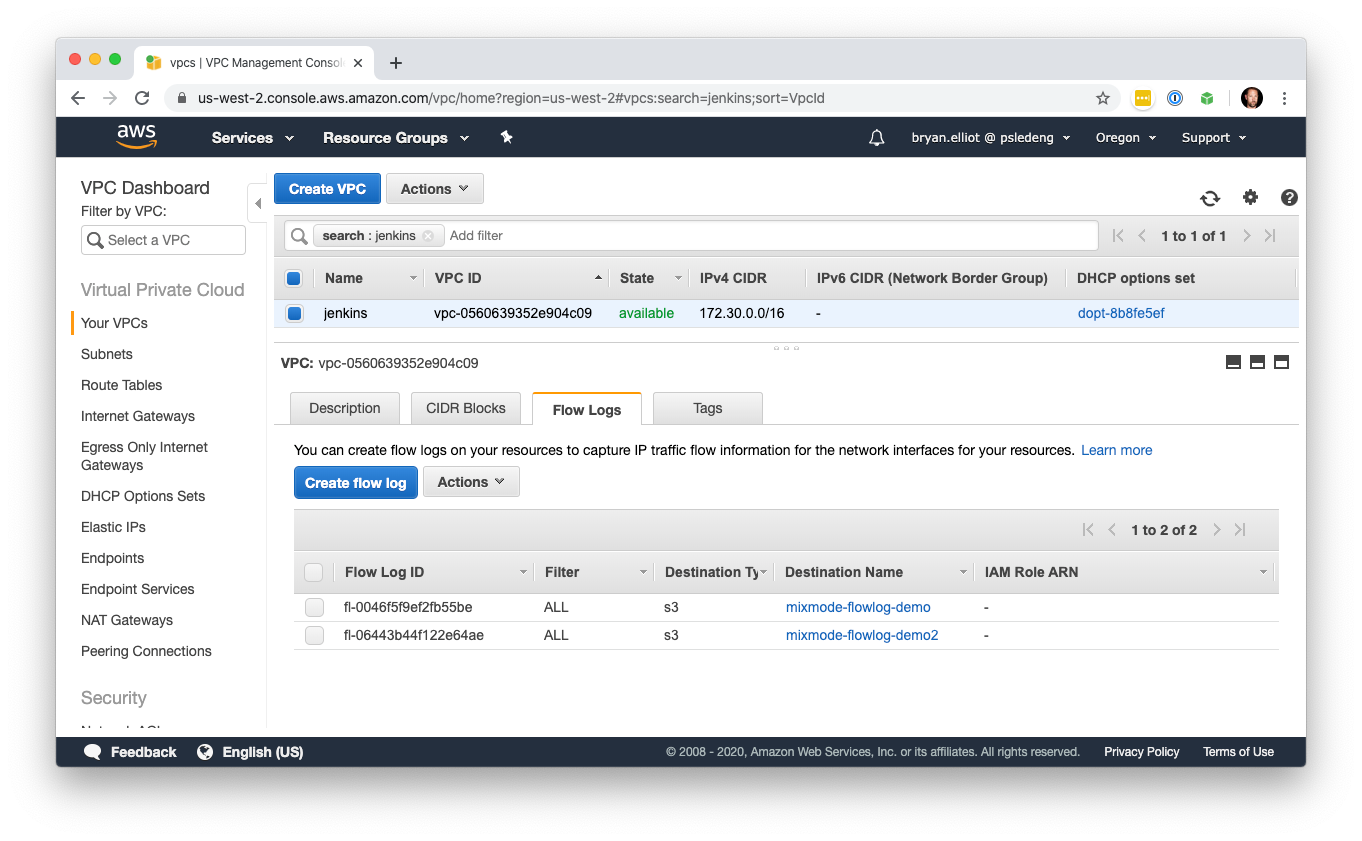
Once set up, AWS VPC Flow Logs can be easily ingested into the MixMode platform, simply by adding a Lambda function to your AWS account (which we provide). This Lambda function watches for Flow Logs to be added to your S3 bucket (by Amazon), and transmits them into the MixMode platform for permanent recording, analysis, machine learning, and interactive discovery and threat hunting using our user interface.
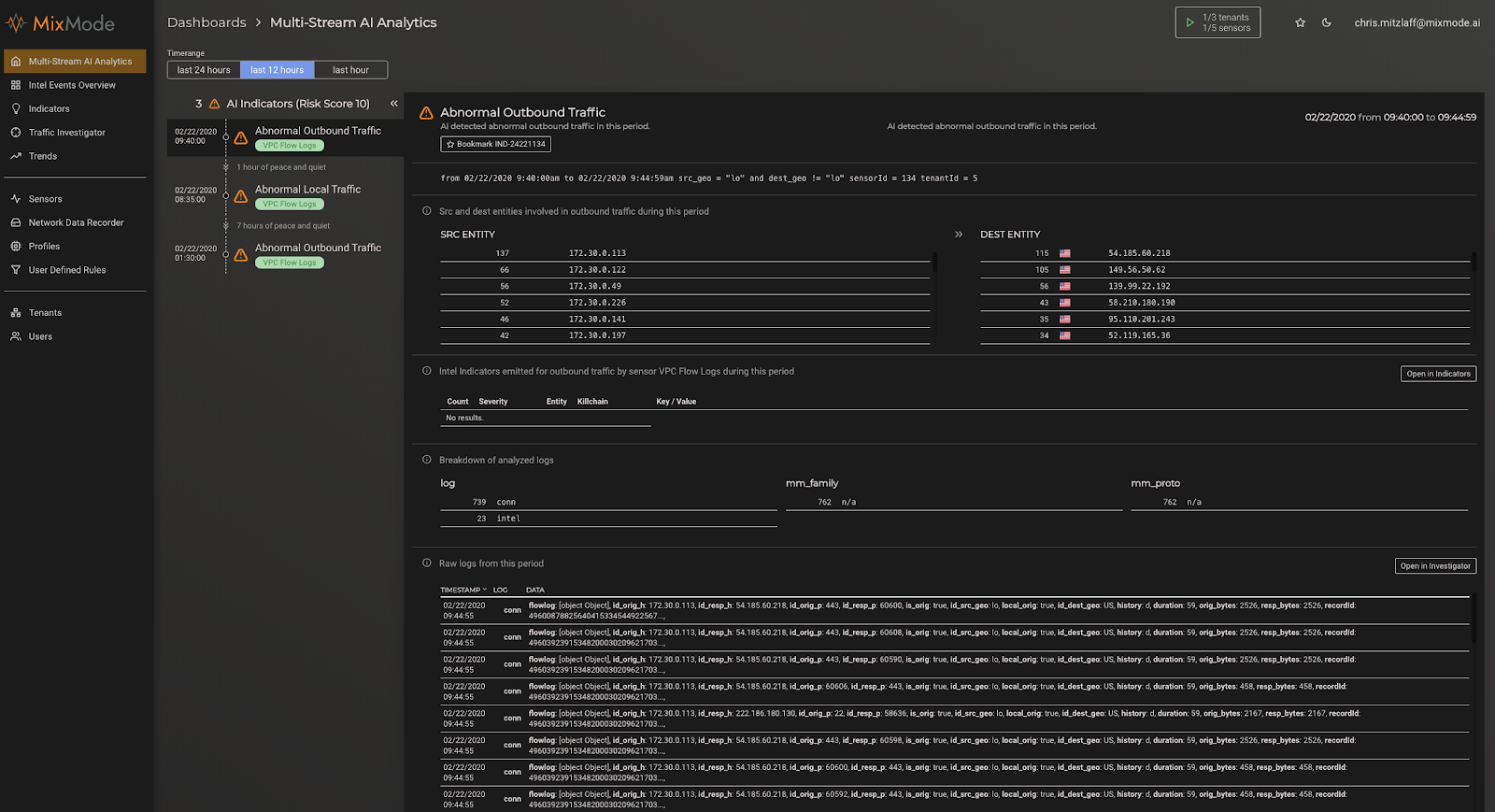
VPC Flow Logs can be correlated with other data across your MixMode deployment, including IP addresses (source and destination), protocols, and other attributes common to all network data sources.

The best way to detect threats across an entire network in the quickest manner is to have complete visibility over every part of that network with a multi-stream platform that can incorporate not only network data, but Cloud Data and SIEM logs as well.
MixMode AI uses its Unsupervised Learning to monitor deviations from the baselines of multiple streams (Cloud, Network Data and SIEM) in order to catch suspicious activity more quickly and effectively than any other security system on the market.
The power of this single view cannot be overstated — it’s an incredible experience to be able to have a birds-eye view, with AI “at your back”, across your entire computing workload.