Unmasking the Challenge: Why Identity Threats are Hard to Detect and How Advanced Behavioral Detection Analytics with AI Can Help
In today’s digital landscape, identity threats have become a pervasive and persistent challenge for organizations. Attackers are increasingly targeting individuals’ identities, credentials, and personal information to gain unauthorized access, steal sensitive data, or perpetrate fraudulent activities. Detecting and mitigating these identity-based attacks is a complex task that requires advanced technologies and a deep understanding of evolving attack techniques. In this blog post, we will explore why identity threats are so hard to detect, the limitations of legacy threat detection solutions, the types of identity threats organizations face, recent examples of identity breaches, and the role of Advanced Behavioral Detection Analytics Enhancing with AI in stopping identity-based attacks.
IAMs are Not Enough
Identity Access Management (IAM) and Identity Threat Detection are two distinct but interconnected concepts. IAM focuses on managing and controlling user access to systems, applications, and resources within an organization. It involves user provisioning, authentication, authorization, and access governance. On the other hand, Identity Threat Detection goes beyond IAM by actively monitoring and analyzing user behaviors, access patterns, and contextual information to identify potential identity-related threats or security incidents. While IAM is crucial for establishing a solid foundation of access controls, Identity Threat Detection provides the necessary visibility across an attack surface and proactive defense against emerging identity-based attacks.
Limitations of Legacy Solutions
Legacy threat detection solutions, such as signature-based systems or rule-based approaches, are ill-equipped to effectively detect and respond to identity threats. These solutions rely on predefined patterns or known signatures of previously identified threats, making them ineffective against new and evolving attack techniques. Identity threats often involve sophisticated social engineering tactics, zero-day vulnerabilities, or insider threats that lack specific signatures. Legacy solutions struggle to detect lateral movement to keep pace with these dynamic threats, resulting in missed attacks and increased vulnerability.
Types of Identity-Based Threats
There are many types of attacks targeting the identity layer:
- Phishing Attacks: Phishing attacks involve fraudulent attempts to trick individuals into revealing sensitive information, such as usernames, passwords, or financial details. Attackers often impersonate trusted entities through emails, websites, or phone calls, making it challenging to differentiate between legitimate and malicious communications.
- Credential Theft: Attackers employ various techniques, such as keyloggers, password cracking, or data breaches, to steal valid credentials. Compromised user credentials can then be used to gain unauthorized access to systems, accounts, or sensitive data.
- Account Takeovers: Account takeovers occur when attackers gain unauthorized access to a user’s account by exploiting weak passwords, stolen credentials, or password reuse. Once inside, attackers can manipulate or misuse the account for malicious purposes.
- Insider Threats: Insider threats involve employees or authorized individuals who misuse their access privileges to steal sensitive data, sabotage systems, or compromise security. These threats can be challenging to detect as insiders often have legitimate access and knowledge of the organization’s systems and processes.
Recent Identity-Related Breaches
Identity-related breaches have dominated the news recently, with high-profile attacks on Okta and MGM taking center stage.
Threat actors breached MGM by exploiting a vulnerability in the company’s Okta environment. This vulnerability allowed the attackers to access privileged accounts, which they then used to move laterally throughout the MGM network and deploy ransomware.
- The attackers gained access to the MGM network through a social engineering attack. They could trick an MGM employee into providing them with login credentials.
- Once they had access to the network, the attackers moved laterally and gained access to privileged accounts.
- The attackers then used these privileged accounts to deploy ransomware on MGM’s systems.
The MGM breach is a reminder that even the largest and most well-funded organizations are vulnerable to cyberattacks. Organizations need strong security measures, including implementing multi-factor authentication (MFA) for all accounts, regularly patching vulnerabilities, and monitoring IAM systems for suspicious activity.
Identity Threat Detection and Response
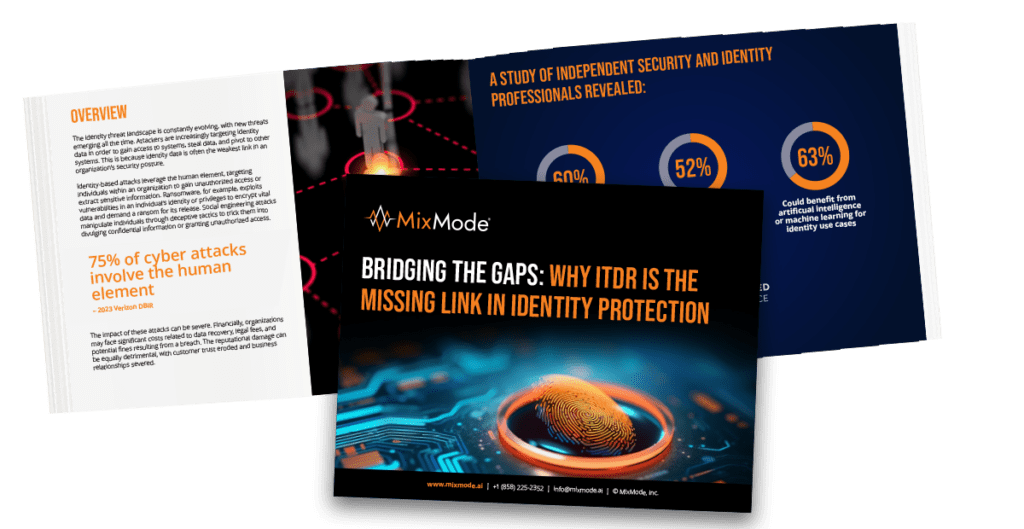
Gartner defines identity threat detection and response (ITDR) as “a security discipline that encompasses threat intelligence, best practices, a knowledge base, tools, and processes to protect identity systems.” ITDR works by implementing detection mechanisms, investigating suspicious posture changes and activities, and responding to attacks to restore the integrity of the identity infrastructure.
ITDR is needed to defend against identity-based attacks because identity is the new perimeter. In the past, organizations focused security concerns on protecting their networks and devices from attack. However, malicious actors increasingly target identities to gain access to sensitive data and systems, presenting new security challenges.
ITDR can help organizations to defend against identity-based attacks by:
- Detecting suspicious activity: ITDR tools can monitor identity systems for suspicious activity, such as abnormal login attempts, changes to user permissions, and unusual access to sensitive data.
- Investigating incidents: Once suspicious activity has been detected, ITDR tools can help organizations investigate the incident and determine the root cause.
- Responding to attacks: Once the root cause of an incident has been determined, ITDR tools can help organizations respond to the attack and mitigate the damage.
ITDR is an integral part of any organization’s security strategy. By implementing ITDR, organizations can help to protect themselves from identity-based attacks and reduce the risk of data breaches.

Adopting Advanced Behavioral Detection Analytics
To effectively detect and stop identity-based attacks, organizations need to adopt advanced behavioral detection analytics enhanced with AI. This approach leverages AI algorithms, machine learning, and behavioral analytics to analyze vast amounts of data, identify patterns, and detect anomalies that may indicate identity threats. By continuously monitoring user behaviors, access patterns, and contextual information, AI-driven solutions can detect suspicious activities, unauthorized access attempts, or compromised identities in real-time.
AI-powered solutions offer several advantages over legacy systems. They can adapt and learn from evolving attack techniques, detect unknown threats, reduce false positives, and provide actionable insights to security teams. By combining the power of AI with behavioral analytics, organizations can gain a comprehensive understanding of normal user behaviors and quickly identify deviations that may indicate identity threats.
Using Identity Threat Detection to Combat Ransomware
Identity threat detection solutions can play a role in combating ransomware attacks. While their primary purpose is to detect and prevent identity-related threats, they can contribute to overall cybersecurity efforts, including ransomware defense, in the following ways:
- User Behavior Monitoring: Identity threat detection solutions often monitor user behavior, such as login patterns, access privileges, and data usage. By analyzing user behavior, these solutions can identify suspicious activities that may indicate a ransomware attack. For example, if a user suddenly starts accessing many files or exhibits unusual file modification behavior, it could be a sign of ransomware activity.
- Privilege Management: Ransomware often spreads by exploiting user privileges and accessing sensitive files or systems. Identity threat detection solutions can help manage and enforce proper privilege levels, ensuring that users only have access to the resources they need. By limiting unnecessary privileges, the attack surface for ransomware can be reduced, making it harder for the malware to propagate.
- Multi-Factor Authentication (MFA): Implementing MFA as part of an identity threat detection solution can significantly enhance security against ransomware attacks. By requiring additional authentication factors, such as a one-time password or biometric verification, MFA adds an extra layer of protection against unauthorized access. This can prevent attackers from gaining control over user accounts and spreading ransomware.
- User Education and Awareness: Identity threat detection solutions often provide user awareness and training features. By educating users about the risks of ransomware and best practices for cybersecurity, these solutions can help prevent ransomware attacks from succeeding. Users aware of the dangers and know how to identify and report suspicious activities are less likely to fall victim to ransomware.
- Integration with Security Ecosystem: Identity threat detection solutions can integrate with other security tools and systems, such as endpoint protection platforms and network security solutions. By sharing threat intelligence and collaborating with these systems, they can contribute to a comprehensive defense against ransomware attacks. For example, if an identity threat detection solution detects suspicious behavior, it can trigger an alert to initiate incident response actions, such as isolating affected systems or blocking network communication.
MixMode: Solving for Identity-Based Attacks
Identity threats pose significant challenges for organizations, requiring advanced detection and response capabilities to mitigate risks effectively. Legacy security tools and threat detection solutions fail to address the dynamic nature of identity-based attacks.
MixMode’s Identity Threat Detection and Response Solution provides real-time monitoring of your identity infrastructure, capable of ingesting and analyzing large volumes of diverse data from multiple systems.
MixMode ITDR continuously monitors your environment and correlates behavioral, access, and log data to proactively identify threats targeting credentials, privileges, cloud entitlements, and the systems that manage them.
- Real-time Threat Detection: MixMode utilizes proprietary AI to analyze network data and identify abnormal behaviors, malicious activities, and indicators of compromise related to identity threats. This AI-driven approach enables MixMode to detect sophisticated attacks that may go unnoticed by traditional rule-based systems.
- Comprehensive Visibility: MixMode provides real-time visibility into network traffic and identity log data )from IAMs like Okta and Azure AD), allowing organizations to monitor user behaviors, access patterns, and contextual information. This visibility enables the early detection of identity threats, enabling organizations to respond swiftly and mitigate risks before they escalate.
- Autonomous Adaptation: MixMode’s AI algorithms continuously learn and adapt to an organization’s unique network behavior, ensuring that the system stays up-to-date with emerging identity threats. This autonomous adaptation capability reduces the need for manual intervention and constant updates, making it easier for organizations to stay protected.
- Context-Rich Alerts: MixMode provides context-rich alerts with detailed information about potential identity threats. These alerts include relevant user behavior data, access patterns, and other contextual information, enabling security teams to quickly understand the nature of the threat and take appropriate action.
By leveraging MixMode, organizations can enhance their ability to detect and mitigate identity threats, safeguard their critical assets, and maintain a strong security posture in the face of evolving security threats.
Reach out to learn how MixMode can help defend against identity compromises and ensure you’re protected.


.png)