Not All Artificial intelligence is created Equal
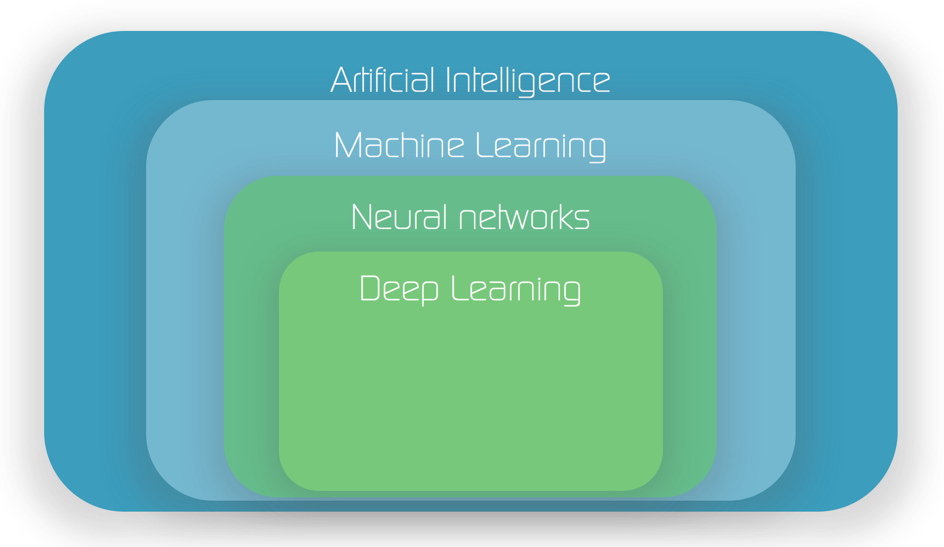
Throughout the tech community, “artificial intelligence” has become a blanket term often used to describe any computing process that requires little human input. Tasks like routine database functions, scheduled system scans, and software that adds automation to repetitive actions are regularly referred to as AI.
In truth, AI can play a part in these processes, but there are some major differences between basic machine learning and true AI.
It is vital to consider this distinction when reading blogs and articles that try to outline the key aspects of AI and present an objective analysis of the shortcomings inherent to certain types of AI.
MixMode has made a name for itself as an AI-Powered network traffic analysis leader with the most powerful and advanced AI in the cybersecurity industry, and want to share a few considerations to keep in mind when researching products claiming to use AI and ML.
Not all artificial intelligence is created equal.
Supervised vs. Unsupervised AI
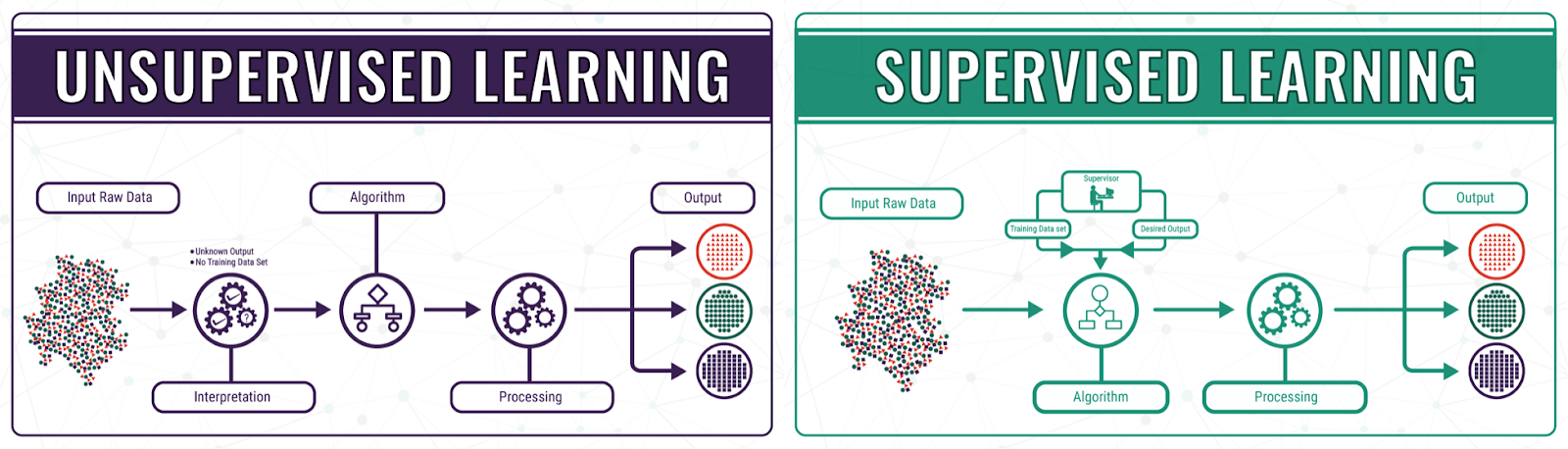
Advances in machine learning over the past several years, enhancing processes like facial recognition technologies and revolutionizing the self-driving car industry. These “supervised learning” AI applications are remarkable and signal a societal shift in how humans interact with technology.
However, supervised learning is limited in its ability to handle complex, sprawling tasks like discovering the threats lurking on an organization’s network. Supervised AI can only locate specific threats it has seen or labeled before. Unsupervised learning, on the other hand, never ceases in its search for network anomalies.
The Vital Distinctions Between Labeling and Learning
Supervised learning relies on labeling to “understand” information. Once a SecOps professional has labeled data, supervised learning can “recognize” it and respond according to set parameters. A supervised learning platform might automate a message alerting the security team to a concerning data point. However, it cannot label data on its own.
These limitations would be sufficient for securing networks if SecOps teams knew exactly what to tell supervised learning platforms to find. The reality is that cybersecurity doesn’t work that way. Bad actors are always a few steps ahead of the game, coming up with new methods of attack all the time.
Unsupervised AI to the rescue.
No matter what tactic a hacker uses, unsupervised machine learning AI seeks out patterns outside the network norm. SecOps teams can immediately focus on issues as they arise and even swat down attacks before they cause damage or lead to data loss.
Our Thoughts on the AI Startup Market
When it comes to chatter within the VC and Startup community about startups claiming to have a foundation in AI and deep learning (and their opportunity for success in the market), there are four market claims that MixMode CTO and Chief Scientist, Igor Mezic, would like to address.
Mezic developed the patented unsupervised AI that drives the MixMode platform and shares his thoughts here:
1. Deep learning costs a lot to compute for marginal payoffs.
The computational cost related to training can quickly offset the potential benefits of deep learning. Mezic explains that this cost is a concern only when deep learning is used exclusively to reach customer data. Mezic developed the MixMode platform as a layered approach — an unsupervised, or semi-supervised architecture that yields efficiency in computation, widening profit margins.
Additionally, Mezic says, MixMode can train AI via an efficient seven-day initial period. (Check out our most recent video on Network Baselines here.) From there, the AI keeps learning in an unsupervised manner.
Mezic stresses that the MixMode’s semi-supervised algorithms require less human touch, as well, further driving down expenses. “MixMode requires little labeling and depends on customer interactions with the AI rather than internal MixMode resources,” he explains.
2. Machine learning AI startups generally have no moat or meaningful special sauce.
Tech differentiation is difficult to achieve in the cluttered AI landscape. Mezic points to MixMode’s Third Wave class of AI algorithms that are not commoditized. Mezic says, “the MixMode algorithm has led to several implementation patents and substantial additional network effects that enhance defensive IP moats.”
Some claim that each organization on the customer side might have different data and associated requirements. However, enterprise networks are similar in the type of data they produce. Thus, Mezic argues, “a single algorithm can be applied to all such data without substantial modifications on the ingest side.”
3. Machine learning startups are mostly services businesses, not software businesses.
Many machine learning startups are service-oriented. However, Mezic makes a distinction between the norm and what MixMode brings to the table.
“We have structured the AI here to apply to all the types of data that occurs in our narrow, specifically defined problem,” he explains. This level of specificity provides much more robust network protection over services that approach data handling generically and only according to a specific set of requirements.
4. Machine learning will be most productive inside large organizations that have data and process inefficiencies.
Some industry experts claim large organizations have inherent data and process inefficiencies, which make them ideal targets for meaningful machine learning benefits but that the process of adopting machine learning AI is too arduous and time-consuming. However, Mezic says the security data in many large organizations is well-structured and organized, which contributes to a streamlined system set-up.
In the end, while startup industry experts make valid points about the current state of AI-enhanced services and software, these arguments must be evaluated with an overarching understanding that “AI” can be a limiting term. MixMode’s unstructured machine-learning AI is distinct, and far more powerful, than garden-variety, supervised AI offerings.
Learn more about how MixMode is helping organizations detect, analyze, visualize, investigate, and respond to threats in real-time.


