Aligning an Organization’s Attack Surface to Detection Surface is Key to Adversary Defense in Today’s Cloud Era
In the traditional IT infrastructure, perimeter-based defense was the norm, and detecting attacker activity was limited to network and endpoint-based activity and Active Directory. However, with the Cloud Era, the IT asset estate has expanded, and there is a diverse set of attack surfaces to defend. The term “attack surface” describes the growing IT asset estate, but there is no parallel term to describe where we can detect or respond to attacker activity.
Until now, the attack surface was the closest match to true perimeter-based defense on traditional infrastructure such as laptops, servers, workstations, and on-premises network infrastructure.
Forrester recently introduced Detection Surface, a cybersecurity defense that parallels attack surface, focusing on the assets where attacker activity can occur. But what does it mean?
What is Detection Surface?
Detection Surface is a new term defined by Forrester as the IT asset type where the detection of attacker activity occurs. It directly parallels the attack surface, which describes the IT assets within a system. Endpoint detection and response (EDR) can have different detection surfaces, depending on the device type.
In the Cloud Era, many vendors claim to do “cloud detection,” but some things need detection in the cloud. “Cloud detection” includes many technologies, making detection and impact difficult. The Detection Surface helps understand the detection of new technologies for protecting the cloud. It enables us to understand where the detection of attacker activity takes place.
Detection surfaces can vary depending on the vendor and type of security technology used.
Examples of Detection Surface
Forrester gave some great examples of how to put Detection Surface into practical terms, including:
When discussing EDR, ask: “What detection surfaces do you have coverage for?” They may answer: Windows, Mac, Linux, iOS, or Android. Or they may get more specific: Windows 11 21H2, 10 21H2, 10 Redstone 5, 8.1, 8, 7, Server 2022, Server 2019, etc.
When discussing cloud detection, ask: “What detection surfaces do you have coverage for?” They may answer: containers, an AWS instance, identity, a SaaS application, etc.
When discussing security analytics or UBA, ask: “What detection surfaces do you have coverage for?” They may answer: The detection surface can be a combination of aspects based on what logs you bring into the SIEM — AD, Azure AD, Windows 11, and an Azure instance, for example.
Let’s take MixMode. If we follow this line of thinking MixMode offers a Cloud Detection and Response solution. Our Detection Surface coverage includes AWS, Azure, OKTA, and more.

Where Detection Takes Place
We can all agree the industry does not need another acronym. And while adding anything to detection may help, it does continue to muddy the waters. (I’m looking at you, ZDR.)
As the Forrester blog states, the cloud is the most potent example of this, as many vendors say they do “cloud detection,” in reality, there are many things that can be detected to protect the cloud, from containers to IaaS to SaaS to identity.
Outlining a Detection Surface levels the playing field for vendors to be evenly compared. It also makes it easier for organizations to purchase the tools they need.
The Continuing Need to Understand Your Attack Surface
An attack surface is the total number of potential entry points, including vulnerabilities and endpoints, that hackers can exploit to gain access to the system. In other words, it’s the entire surface area of an enterprise exposed to hacks and security breaches.
Due to advancements in technology, there are more types and numbers of attack surfaces to defend than ever before.
Understanding your attack surface remains vital for enterprise organizations because it enables them to better protect themselves against threats from attackers, cybercriminals, disgruntled employees, and/or competitors. It also helps to identify any gaps in your security program that could open a door for an attacker.
Reducing your attack surface means protecting your organization’s devices and network, which leaves attackers with fewer ways to perform attacks. Your organization’s attack surface includes all the places where an attacker could compromise your organization’s devices or networks. The external attack surface extends far beyond an organization’s assets. It often includes suppliers, partners, unmanaged personal employee devices connected to company networks or assets, and newly acquired organizations. Consequently, being aware of external connections and exposure is critical to mitigate potential threats.

How Does Logging Fit In?
Logging and detection are two distinct concepts. Logging refers to the act of recording events or actions that occur within a system, while detection refers to the process of identifying and responding to potential security threats.
Logging is important because it allows organizations to review past events and track user activity, aiding investigations and audits. However, logging alone is not sufficient for detecting security threats. Detection requires specialized tools and techniques to identify abnormal behavior or patterns that could indicate a potential attack.
While logging is a valuable tool for maintaining system integrity and accountability, it’s important to understand it is not the same as detection, which is critical for identifying and responding to security threats in real-time. Both logging and detection play essential roles in cybersecurity, with logging providing the data source for detection systems to perform their analysis and identification tasks.
MITRE ATT&CK vs. Detection Surface
Detection Surface is an important concept that helps us better understand where attacker activity is detected in the IT infrastructure. But how important is knowing the tools and techniques these attackers use? I’d say very, which is why my brain went immediately to the MITRE ATT&CK Framework. While the MITRE ATT&CK framework helps understand tactics and techniques threat actors use, it does not directly show an organization’s detection surface. Together, along with understanding your attack surface, can be powerful in helping organizations identify gaps in their defenses and improving their security posture.
Monitoring Your Infrastructure
I agree that understanding your Detection Surface is essential. But I think there’s more to learn from Forrester’s initial write-up. Like an Attack Surface, a Detection Surface will be continuously growing. What may be considered your detection surface today may not be the same tomorrow. Your detection surface will expand.
And shouldn’t a threat detection platform monitor an entire attack surface since it can all be targeted by an attacker?
Why Care About Detection Surface?
Organizations should care about Detection Surface because, like ASM, it refers to the potential areas that threat actors can exploit. The larger the attack surface, the more vulnerable an organization is to cyber-attacks.
By understanding and minimizing where attacker activity occurs, organizations can reduce their risk of cyber-attacks and ensure the protection of their most critical assets.
MixMode: Real-time Threat Detection for Your Detection Surface
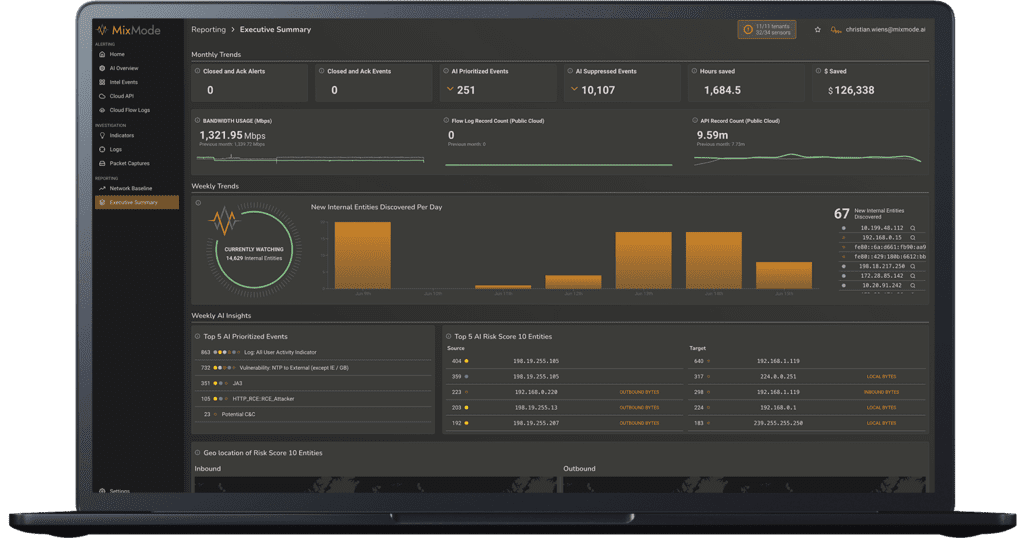
MixMode was built to meet the comprehensive detection needs of the modern enterprise across cloud, hybrid and on-prem deployments. The MixMode Platform is a real-time dynamic threat detection and response platform that identifies novel and known attacks at scale. MixMode helps enterprise security teams monitor their detection surface in real-time to detect attacker activity and surface-relevant threats.
The MixMode Platform is the world’s first commercially available cybersecurity platform built on Third Wave AI (as defined by DARPA). The Platform can be seamlessly installed in minutes, immediately acclimating itself to autonomously learn, understand, adapt, and evolve without relying on rules, training, or human interaction.
MixMode’s AI, which is self-learning and does not require humans to train or tune it, offers tremendous value to security analysts by:
- Watching the entire detection surface on cloud and network and surfacing threats that may bypass traditional rules or signatures
- Correlating threats across different attack surfaces and looking for patterns in attacks
- Reducing the number of false positives across the detection surface allowing analysts to keep an eye where they need to and focus on the threats that matter
The result is a truly autonomous defense system that dramatically enhances security programs, detects threats others miss in real-time, and delivers tangible business outcomes in a matter of days.
Reach out to learn more.


.png)