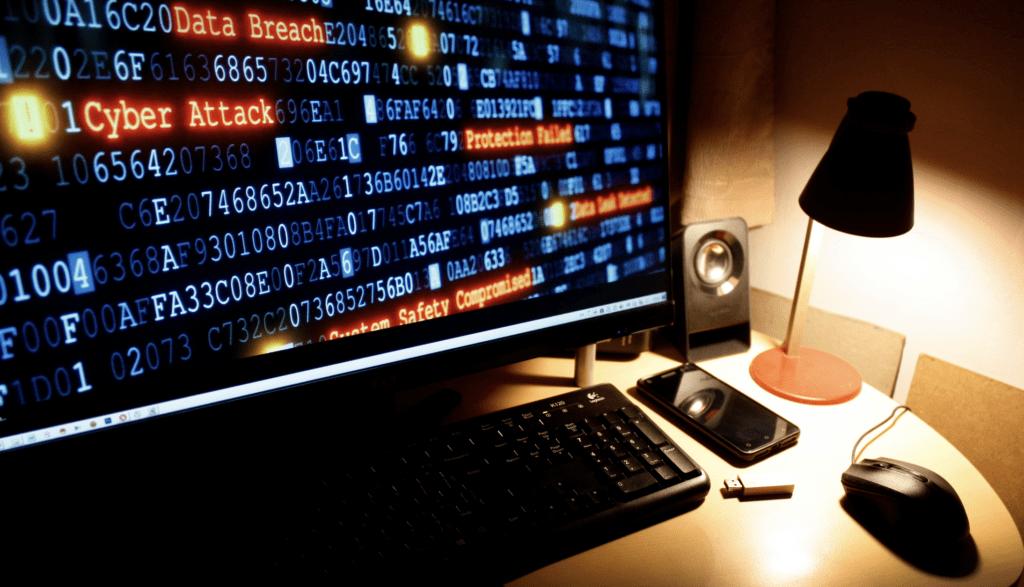
2023: Top 10 Cybersecurity Stats That Make You Go Hmmmmm
Alright, listen up, you cypherpunks and data desperados! Rob Burgundy here, stepping out of the anchor booth and into the wild frontier of cybersecurity stats. Forget your cat vids and TikTok trends, because these numbers are hotter than a chili cook-off in Hades.
2023: Top 10 Cybersecurity Stats That Make You Go Hmmmmm Read More →