MixMode: Revolutionizing Threat Detection and Prioritization in Cybersecurity
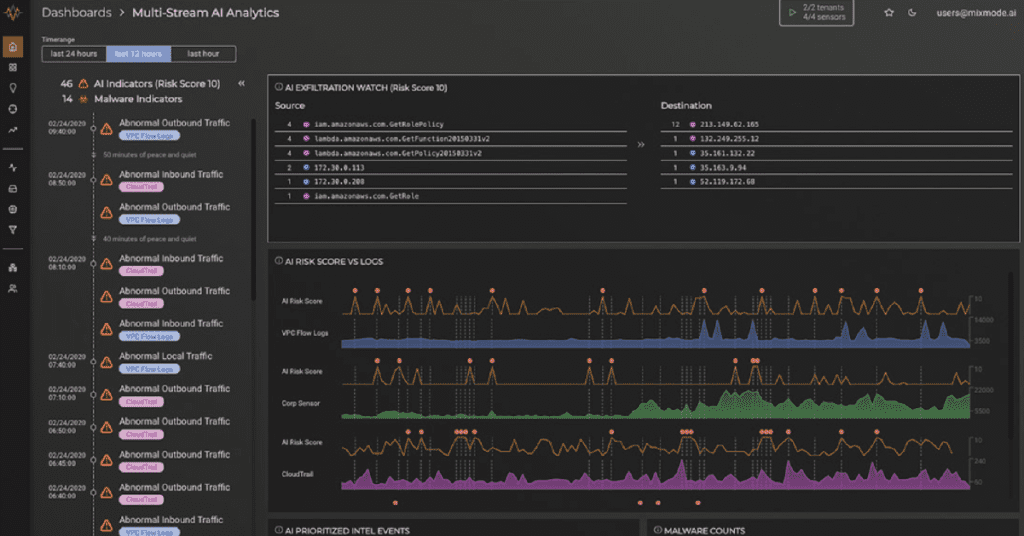
Enter MixMode. The MixMode Platform is a cutting-edge cybersecurity solution that is changing the game in threat detection and prioritization. The MixMode Platform offers a powerful alternative to traditional security tools by leveraging advanced artificial intelligence and a unique data analysis approach.
MixMode: Revolutionizing Threat Detection and Prioritization in Cybersecurity Read More →