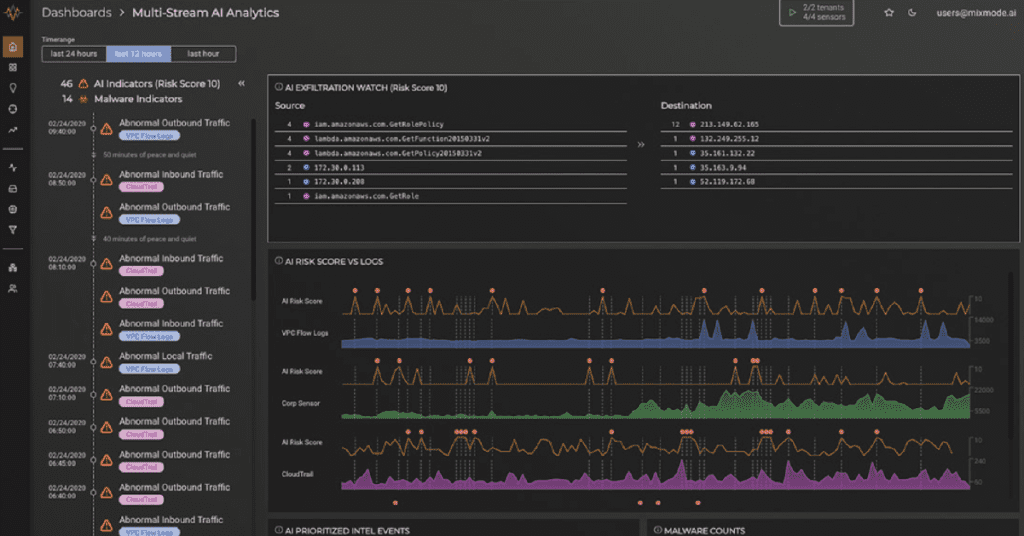
The Aggregation Model is Falling Short
The following is an excerpt from our recent whitepaper, “Why Traditional Cybersecurity Tools Cannot Defend Against Zero-Day and No Signature Attacks,” in which we dive into how traditional cybersecurity tools work, why this fundamentally limits them from being able to detect zero-day or previously unknown attacks, why the industry standard for breach detection is around […]
The Aggregation Model is Falling Short Read More →