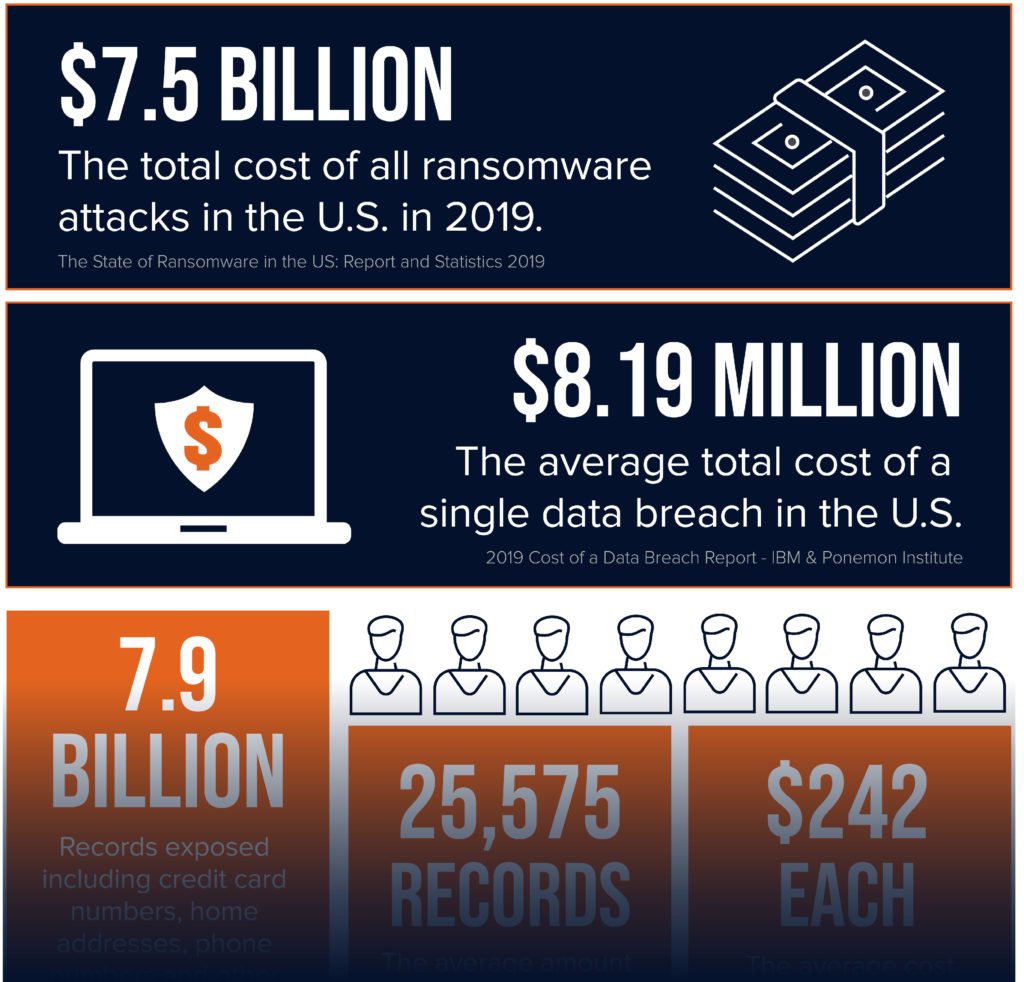
Top Data Breaches in 2022 and 2023 Point to Increases in Phishing and Ransomware
The hits just keep on coming in the world of headline-grabbing data breaches. Threat actors kept busy in 2022 and right on into the new year, with several notable data breaches already making news in 2023.
Top Data Breaches in 2022 and 2023 Point to Increases in Phishing and Ransomware Read More →