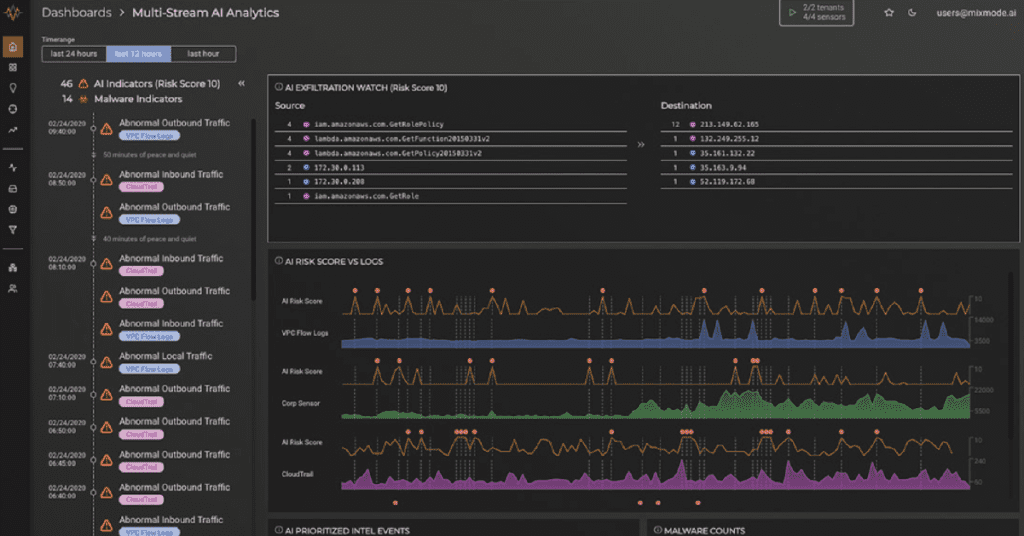
MixMode in the Real World: Customers Turn to MixMode Frustrated and in Search of a Viable SIEM Alternative
SIEM has failed to meet the needs of enterprises in the modern threatscape. One huge reason for this is that over time, most organizations will come to the sad realization that they will never achieve a full enterprise deployment of their SIEM. By its very nature, SIEM is always “in process.” It’s not unusual for an organization to have an SIEM in process for a full decade.