Unveiling the Power: A Strategic Look at the Benefits of Using AI in Cybersecurity
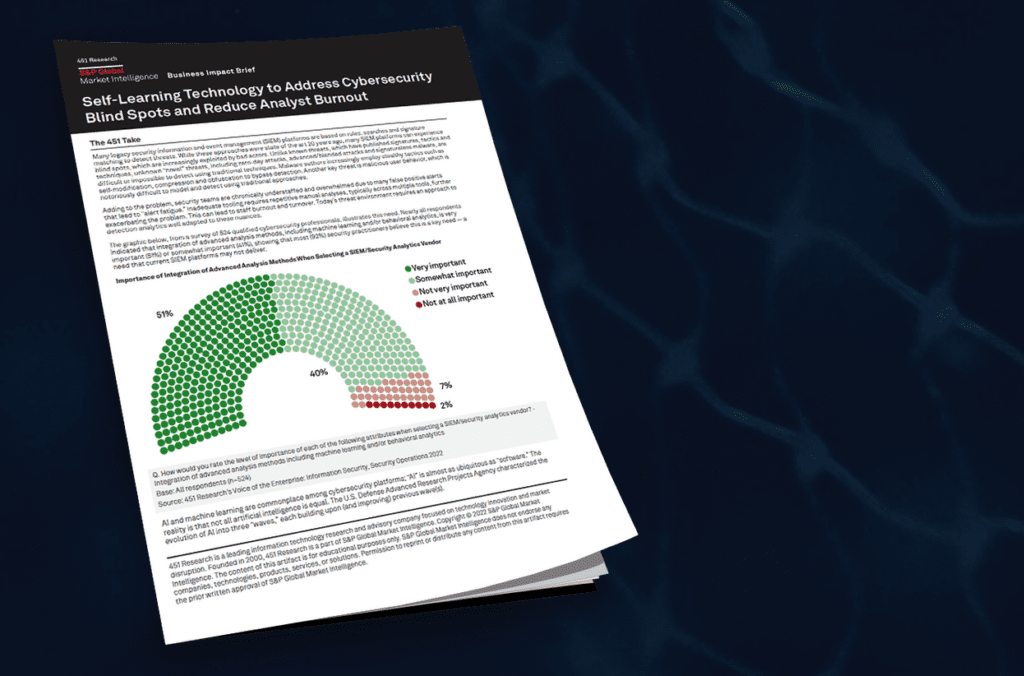
If you’ve followed this blog series, you already know that Artificial intelligence (AI) has become a ubiquitous term, holding immense promise across various industries. Cybersecurity is no exception, with AI poised to revolutionize how organizations defend their data and systems against malicious activity. However, a crucial question remains: Are cybersecurity teams effectively harnessing AI’s potential for maximum security impact?
Unveiling the Power: A Strategic Look at the Benefits of Using AI in Cybersecurity Read More →