MIxmode Blog
The latest stories on Cybersecurity, AI, and everything in between from MixMode
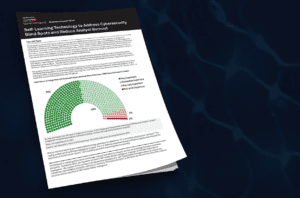
In the report, 451 Research explains why security analytics needs to include advanced Third-Wave AI, which autonomously learns normal behavior and adapts to constantly changing network environments, to address the next generation of cyberthreats and increase SOC productivity.
Read MoreOf all the challenges facing the modern SOC, two stand out among the most persistent and difficult to overcome: an overwhelming volume of false positive alerts and an alarming escalation in zero-day and novel threats that are often imperceptible by legacy systems.
Read MoreThe number of zero-day exploit discoveries hit record numbers in 2021, according to Google Project Zero. Instances of “in-the-wild 0-days” were up nearly double versus 2020, when only 25 0-day exploits were detected. In 2021, the total was 58.
Read MoreExperts have warned that the Russia-Ukraine conflict poses an unprecedented cyber risk for U.S. organizations as well as State and local governments and municipalities.
Read MoreChief Scientist and CTO for MixMode, Igor Mezic, wrote this article for Forbes magazine on the advantages of moving away from a legacy rule-based cybersecurity platform to a third-wave AI platform that can better detect zero-day threats.
Read MoreLog4j is the latest example of a zero-day exploit to be discovered and put a big part of the industry into chaos. Given its wide adoption by developers, the impact of the log4j exploit is quite broad and will take a tremendous amount of time to resolve.
Read Moreou may be surprised to learn that log data is proprietary to each security platform vendor. There is no standard format or even a standard labeling mechanism. Your data only has context within the parameters of your SIEM vendor.
Read MoreHow sure are you that log files represent the best source of information to base your entire Cybersecurity program upon? Log data is the cornerstone of every traditional cybersecurity platform including SIEM (Security Information and Event Management), UEBA (User and Entity Behavior Analytics), and xDR (Detection and Response).
Read MoreWhile we’re seeing more data breaches than in years past, being proactive can make an enormous difference. Head-in-sand is not the optimal position for any modern organization with a network-based infrastructure. Education about the nature of modern data breaches is a great place to start.
Read MoreJust like the SOC analyst, the TVA has to find these threats and remove them as quickly as possible. Let’s say you are tasked with being this TVA agent and are told you need to search all the timelines (an almost infinite number of them) and find all the Loki variants to have them removed.
Read MoreAbout MixMode
MixMode is the first to bring a third-wave, context-aware AI approach that automatically learns and adapts to dynamically changing environments. MixMode’s monitoring platform, PacketSled, better understands network behavior as it adapts to baseline changes and enables both misuse detection and anomaly detection, as well as predictive maintenance. Used by enterprises and MSSPs for real-time network analysis, threat hunting and incident response, the platform leverages continuous stream monitoring and retrospection to provide network forensics and security analytics. Security teams can integrate PacketSled into their orchestration engine, SIEM, or use PacketSled independently to dramatically reduce false positive alerts and the resources required to respond to persistent threats, malware, insider attacks and nation state espionage efforts.
The company has been named an innovator in leading publications and by security analysts, including SC Magazine, earning a finalist award in 2018 and 2019 for "Best Computer Forensic Solution.” Based in Santa Barbara, with offices in San Diego, the company is backed by Keshif Ventures and Blu Venture Investors. For case studies, continuous product updates and industry news, please visit us at www.mixmode.ai.